In a recent series of events, @TrustPad, a known decentralized finance (DeFi) protocol, has suffered a security breach resulting in an approximate loss of $155,000.
The exploit was carried out through a vulnerability in the protocol’s smart contract, specifically within the staking logic of the LaunchpadLockableStaking contract.
Key Details of the Exploit
Table of Contents
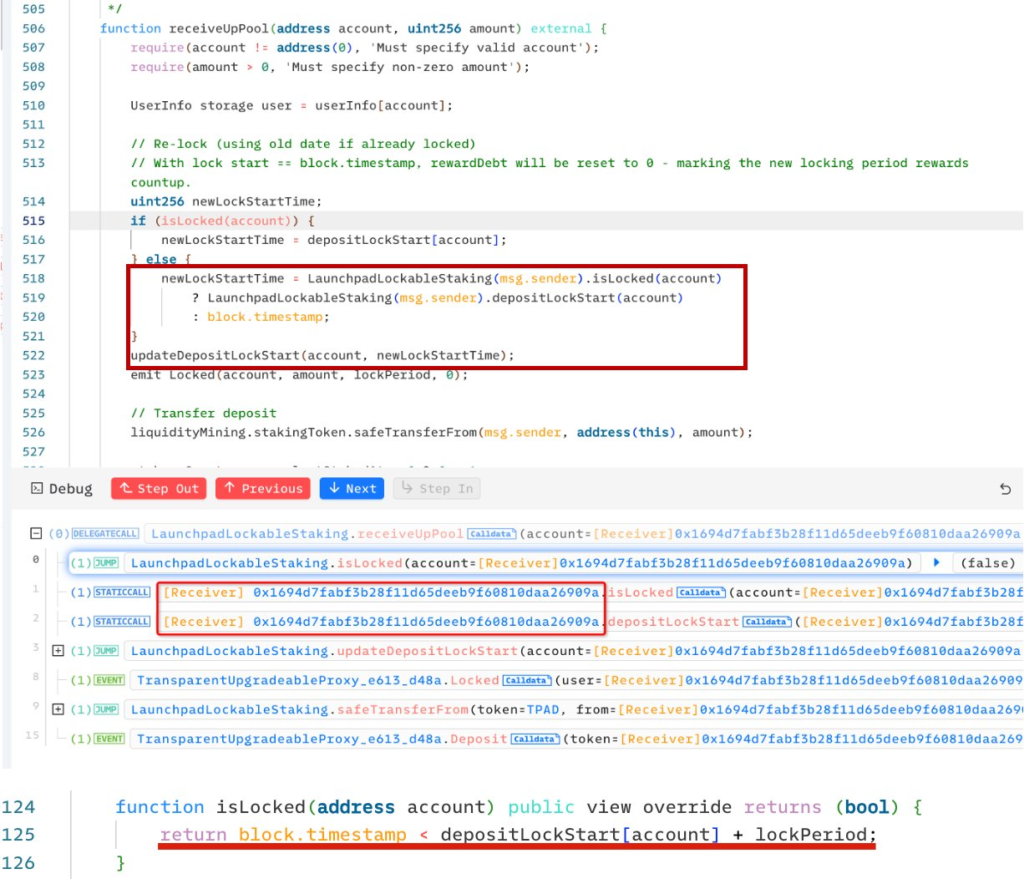
Vulnerability in receiveUpPool Function:
- The receiveUpPool function in the smart contract did not adequately verify the message sender (msg.sender).
- This oversight allowed the attacker to manipulate a key variable, newlockstartTime, which is integral to setting the staking period.
Exploitation Strategy
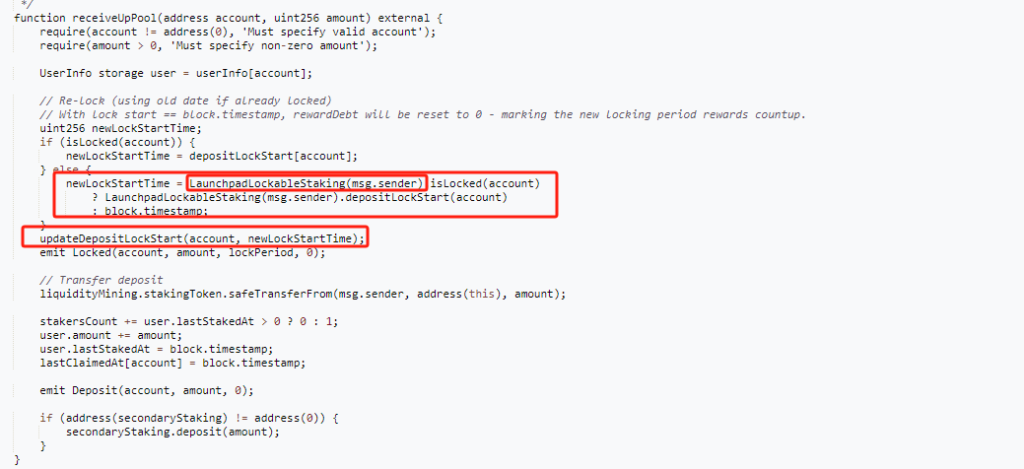
- The attacker executed the receiveUpPool() function, followed by withdraw() in a repeated cycle to harvest staking rewards prematurely.
- Normally, these rewards should be locked for a specified duration, but the exploit enabled the attacker to circumvent this locking mechanism.
Conversion of Rewards
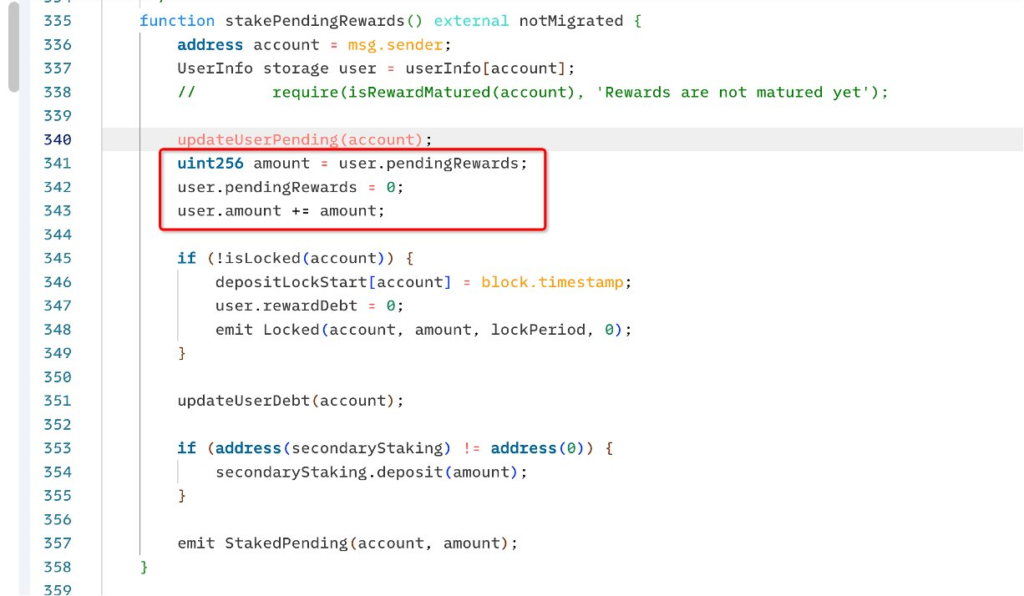
Utilizing the stakePendingRewards function, the attacker converted the improperly harvested pending rewards into staked amounts.
This was a pivotal step that allowed the withdrawal of the rewards in the form of TPAD tokens.
Profit Realization
After converting the pending rewards into staked amounts, the attacker then withdrew the staked rewards.
The TPAD tokens obtained through this process were subsequently sold for financial gain.
Response from TrustPad
Following the incident, TrustPad has issued official statements via social media urging users to cease all trading of TPAD tokens immediately.
The TrustPad team is currently investigating the breach and has promised to issue a detailed response upon the conclusion of their analysis. They have reassured their users that a snapshot of wallet balances will be taken to ensure the security of funds.
TrustPad has cautioned all holders and traders to refrain from selling or buying TPAD tokens until further notice.

