Overview
Table of Contents
On June 08, 2022, GYM Network, a BSC-based yield aggregator operating on Alpaca Finance, suffered a significant security breach, resulting in a loss of approximately $2.1M (~7.5k BNB).
This incident occurred due to the exploitation of a lack of authentication in a newly added smart contract function, depositFromOtherContract(), within the “Claim and Pool” feature in their updated Single Pool Contract.
The exploit led to the substantial theft and subsequent sell-off of GYMNET tokens, causing a dramatic crash in their value.
About GYM Network
GYM Network, a DeFi Aggregator Investment System, focuses on combining superior yields with significant rewards for its users, thereby streamlining access and saving valuable time.
The platform is unique in the sense that it is user-owned and operates democratically: each user’s voting power is directly tied to their holdings of GYMNET tokens.
This structure enables users to actively participate in the governance of the network by proposing and voting on “Exercise Routines,” which are essentially proposals aimed at enhancing and improving the system.
Root Cause Analysis of the GYM Network Hack
Overview of the Vulnerability
The hack of the GYM Network primarily stemmed from a critical vulnerability in their depositFromOtherContract() function.
This function lacked the necessary authentication checks, a flaw that the attacker exploited to create fraudulent deposit records. This was possible without transferring any actual tokens to the contract, thus bypassing the system’s security measures.
Introduction of the Vulnerable Function
Context of Addition: The vulnerable function was part of an update in the GYM Network’s smart contract. It was added after the project’s last audit, meaning it was not covered in the audit scope.
GYMNET Token Contract: 0x0012365f0a1e5f30a5046c680dcb21d07b15fcf7
The updated contract with the vulnerable function can be found at https://bscscan.com/address/0x0288fba0bf19072d30490a0f3c81cd9b0634258acode.
Feature Details: The feature in question, termed the “Claim and Pool” functionality, was introduced into the Single Pool Contract of the GYM Network, which is a BSC-based yield aggregator built on Alpaca Finance.
GYMNET single pool contract: https://bscscan.com/address/0x0288fba0bf19072d30490a0f3c81cd9b0634258a
Time of Addition: The function was added to the system two days before the exploit.
Nature of the Bug: The primary issue with the function was the lack of caller verification, a critical oversight that allowed the attacker to increase their balance in the system without making any actual payment.
Audits and Security Measures
Previous Audits: GYM Network had undergone two audits by third-party auditors in the month preceding the hack. However, these audits did not cover the newly introduced feature that contained the vulnerability. Conceptual Explanation
Exploited Vulnerability: This incident is a classic example of a vulnerability arising from insufficient authentication in smart contract functions. Such vulnerabilities allow unauthorized parties to perform actions that should typically require validation or a transfer of assets.
This analysis highlights the importance of regular and comprehensive security audits, especially after any significant updates or additions to the smart contract functionalities, to prevent similar incidents in the future.
Detailed Analysis
Overview of the Exploit
The attacker strategically exploited the depositFromOtherContract() function in the GYM Network’s smart contract. This function was vulnerable due to the absence of a transfer function, which is typically responsible for moving a user’s deposit into the contract.
Consequently, this flaw allowed the attacker to create deposit records without actually transferring any tokens to the contract.
Execution of the Attack
- Initial Setup: The attacker deployed multiple contracts specifically designed to exploit the vulnerability.
- Exploitation Technique: Using the contracts, they repeatedly set a deposit amount of 8,000,000 GYMNET tokens. The missing transfer function in
_autoDepositallowed this action without any real token transfer. - Creation of False Records: The attacker used the flaw to ‘deposit’ 8,000,000 GYMNET tokens multiple times, creating false deposit records in the process.
Hack Transactions
0x171a448161f2c438cca0502599a6784561d11099c9218e2125c5f3c7a6705dd30x91f5e625447da3e7d0d409d5c7762c94c4d5793ab34430b81a9889e5ef9f37dd0x12970f3962b4bacd01bb4e3dc086804e4e5861134db5dd80d7e4671aa7f23d16- 0x8432c1c6613995eeea8a3ae2cfeb9577913db6b7b35dbe26a8c56c02066096e6
Exploiter’s Address: 0xb2c035eee03b821cbe78644e5da8b8eaa711d2e5
The exploit’s success hinged on the absence of a critical transfer function within the smart contract, which the attacker leveraged to create artificial deposit records and subsequently withdraw substantial amounts in WBNB. The detailed transaction links and the exploiter’s address provide a comprehensive view of the attack methodology.
Stolen Funds Details
Conversion of Stolen Tokens: Once the GYMNET tokens were withdrawn, the attacker converted them into Binance Coin (BNB). In total, the attacker converted the stolen GYMNET into approximately 7,500 BNB.
Movement and Distribution of Stolen Funds
Tornado Cash Transaction: A significant portion of the funds, 2,000 BNB (valued at around $570,000), was sent to Tornado Cash for laundering. This was facilitated through the transaction ID: 0x45fbd778ac22e9b108a72226a84c62db43853640b9591931340118123cf5ec6d.
Remaining Funds on Exploiter’s Address: An amount of 3,000 BNB (approximately $855,000) remained in the exploiter’s Binance Smart Chain (BSC) address, tracked via transaction ID: 0x8432c1c6613995eeea8a3ae2cfeb9577913db6b7b35dbe26a8c56c02066096e6.
Conversion to Ethereum: The remaining 2,500 BNB were swapped for 387 ETH (around $700,000 in value) and subsequently bridged to an Ethereum address.
https://bscscan.com/tx/0x45fbd778ac22e9b108a72226a84c62db43853640b9591931340118123cf5ec6d
Hack Aftermath
Fix Implementation
GYM Network promptly addressed the exploit by introducing a key security enhancement to their smart contract. They added an onlyBank modifier to the depositFromOtherContract function.
This critical update ensures that the function can now be called exclusively by the bank address, thereby closing the loophole that led to the hack.
Address of Patched Contract: https://bscscan.com/address/0x7df0bc661b6a239ae2f41f9548f6b17f7bd8328bcode
Financial Recovery Efforts: In an effort to mitigate the impact on the token’s value, GYM Network utilized its treasury resources. This strategic move was aimed at recovering the price of the GYMNET token as effectively as possible following the exploit.
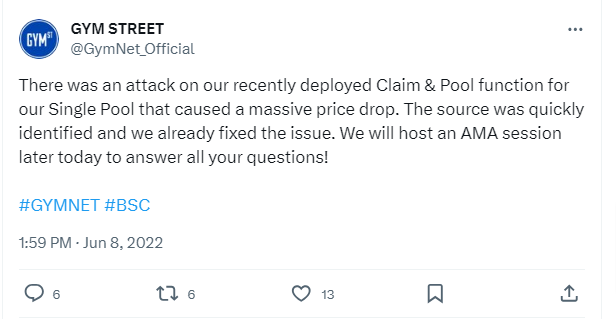
Official Statement and Market Impact
Communication to Users: GYM Network proactively communicated with its community, especially via its Telegram group.
They quickly identified and confirmed the source of the vulnerability, ensuring transparency and maintaining trust with their user base.
Market Reaction: The immediate aftermath of the hack saw a significant drop in the value of GYMNET, with a ~90% decrease as the exploiter offloaded the stolen tokens.
However, following the swift actions the GYM Network team took, the token showed signs of recovery, regaining up to ~70% of its value compared to the pre-hack price.
Mitigation Steps to Avoid Such Hacks
Importance of Comprehensive Auditing
- Thorough Examination of New Functions: This incident underscores the necessity of conducting extensive audits, particularly for newly added functions in smart contracts. Such audits should delve deep into the code to uncover potential vulnerabilities that might not be evident at first glance.
- Engaging Expert Auditors: Organizations like ImmuneBytes specialize in smart contract security. Their expertise can be invaluable in identifying and addressing subtle security issues that could lead to significant vulnerabilities. Collaborating with such expert auditors can ensure a more robust security posture for DeFi projects.
Regular Security Checks and Updates
- Ongoing Auditing Processes: To prevent similar vulnerabilities, it is crucial to establish a routine of continuous auditing and security checks. This process includes regular assessments of existing smart contract functions and scrutiny of any updates or new additions.
- Responsive Adaptation to Emerging Threats: The dynamic nature of blockchain technology and smart contract development means new threats can emerge rapidly. Staying vigilant and adapting security protocols to counter these evolving threats is essential for maintaining system integrity.
Proactive Authentication Measures in Smart Contracts
- Implementing Robust Authentication Protocols: Smart contracts should be designed with strong authentication measures from the outset. This includes ensuring only authorized entities can access functions and incorporating checks to prevent unauthorized interactions.
- User Access Control and Permissions: Defining user roles and permissions clearly within the smart contract can prevent unauthorized access or manipulation. Utilizing multi-factor authentication and other advanced security mechanisms can further enhance the security of smart contract functions.
Conclusion
The GYM Network hack demonstrates the risks associated with smart contract vulnerabilities, particularly in newly added functions. Regular and comprehensive audits, like those provided by companies specializing in smart contract auditing, are crucial in identifying and mitigating such risks to enhance blockchain security.

