Introduction
Table of Contents
On Aug 18, DeFi @ExactlyProtocol, operating on Optimism, encountered a breach resulting in a loss of around $7.3M. A loophole in the DebtManager contract allowed hackers to tweak the market address and evade integral permit checks, leading to the theft of users’ $USDC.
Summary of the Exploit
Attackers made use of an insufficient_check vulnerability in Exactly Protocol’s DebtManager contract. By injecting a fraudulent market address, they successfully skirted the protocol’s permit checks. This opened a door to activate a malicious deposit function, leading to the theft of users’ $USDC. Subsequently, they liquidated users’ assets for illicit gains.
Technical Breakdown
Vulnerability
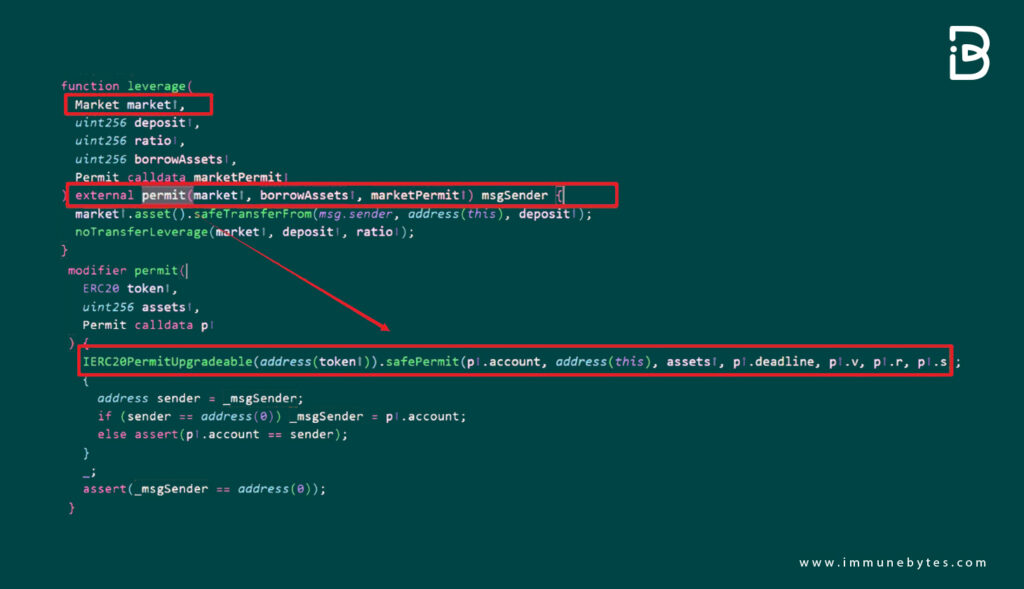
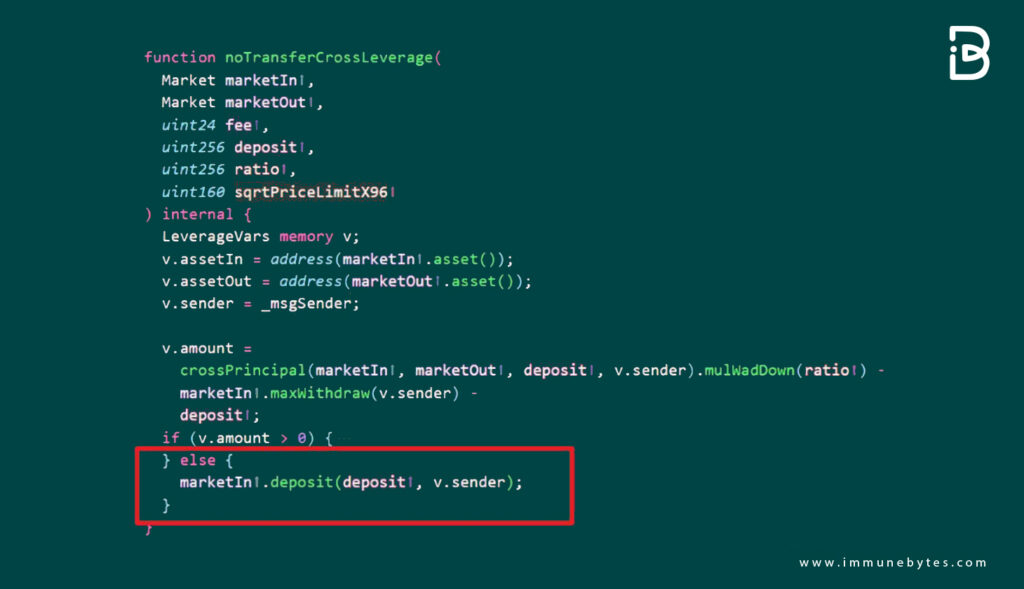
The primary issue was in the DebtManager contract of the Exactly Protocol. It lacked rigorous validation for the market address input.
Attack Methodology
The attacker:
- Manipulated the vulnerability in the `DebtManager` contract
- Inserted a counterfeit market contract address, evading the `permit` checks
- Leveraged this unauthorized access to initiate a harmful deposit function, culminating in the theft of users’ $USDC
- Cashed out user assets to make illicit profits
Reentrancy
Demonstrating profound expertise, the attacker not only bypassed the permit check in the DebtManager contract but also tampered with the _msgSender to impersonate a victim. Using an untrusted external call, they accessed the crossDeleverage function again, stripping collaterals from the _msgSender.
Immediate Response and Investigation
Upon noticing the breach, Exactly Protocol acted swiftly. They acknowledged the incident and started an investigation. Operations were momentarily halted, but provisions were made to facilitate user asset withdrawals.
The protocol is now fully operational, and notably, no liquidations took place. Efforts are ongoing to recover the stolen funds, including establishing communication with the culprits.
Contextualizing the Attack
Market Dynamics
This breach occurred during a wider cryptocurrency market downturn. Established coins, namely XRP, Litecoin (LTC), and Bitcoin Cash (BCH), experienced significant drops. Bitcoin briefly dipped to $25,200 before rallying.
DeFi Sector Vulnerabilities
The Exactly Protocol incident isn’t an isolated case in the DeFi world. Security lapses, especially surrounding technologies like cross-chain bridges, have emerged. Hundred Finance on the Optimism network also faced a hack earlier, resulting in a loss of $7 million in crypto assets.
Attack and Follow-Up Movements
For those interested in a deeper dive, the blockchain transactions tied to the exploit are:
- https://optimistic.etherscan.io/tx/0x3d6367de5c191204b44b8a5cf975f257472087a9aadc59b5d744ffdef33a520e
- https://optimistic.etherscan.io/tx/0x1526acfb7062090bd5fed1b3821d1691c87f6c4fb294f56b5b921f0edf0cfad6
- https://optimistic.etherscan.io/tx/0xe8999fb57684856d637504f1f0082b69a3f7b34dd4e7597bea376c9466813585
Furthermore, the attacker initially secured funds from TornadoCash and bridged them to address 0xe4f3 on Optimism via the Optimism Bridge. The exploit contract was then launched by 0xe4f3, with addresses 0x3747 and 0x4171 executing the attack. Profits were converted to roughly 4324 Ether.
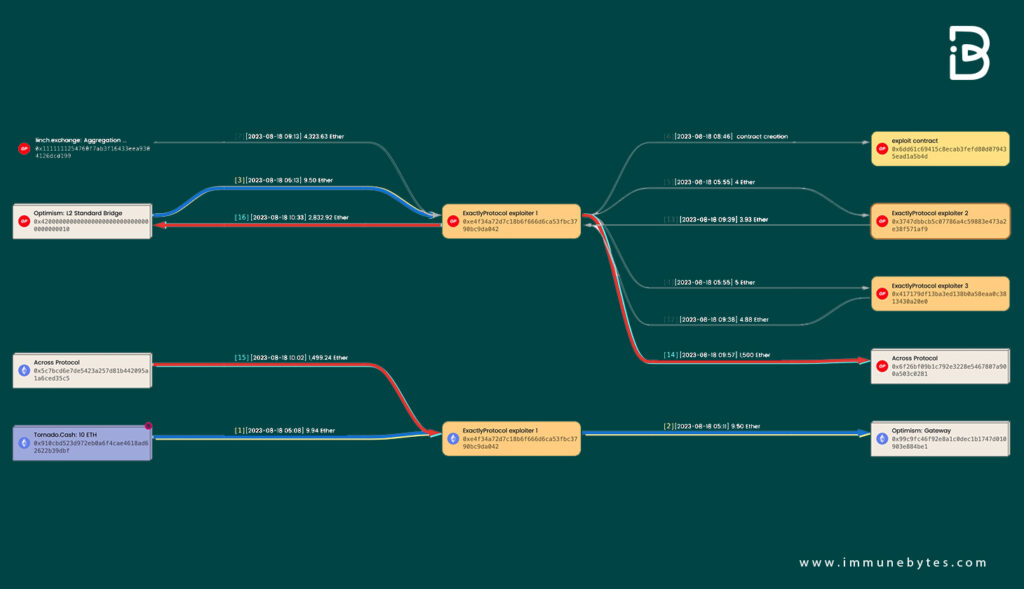
As of now, 1500 Ether has transitioned back to Ethereum via the Across Bridge. Meanwhile, 2833 Ether is en route back to Ethereum through the Optimism Bridge, though the transaction is in the Challenge Period. Surveillance continues on the attacker’s address.
Addresses Associated with the Exploit
- https://optimistic.etherscan.io/address/0x3747dbbcb5c07786a4c59883e473a2e38f571af9
- https://optimistic.etherscan.io/address/0xe4f34a72d7c18b6f666d6ca53fbc3790bc9da042
- https://optimistic.etherscan.io/address/0x417179df13ba3ed138b0a58eaa0c3813430a20e0
Conclusion
The DeFi arena, bursting with potential, also carries inherent risks. Rigorous contract audits, multi-layered security measures, and user education are paramount. As the DeFi world evolves, security must concurrently advance to safeguard a resilient ecosystem. Stakeholders are urged to remain cautious and informed.
An ineffective smart contract audit by unskilled auditors often result into costly exploits. At ImmuneBytes, we believe in treating every vulnerability (minor or critical) with utmost attention and our team of exceptionally adept and experienced auditors ensures that no shortcomings can escape their piercing eyes.

