On September 4, 2021, DAO Maker’s vesting contract was exploited, resulting in a significant loss of funds. This report provides a detailed account of the hack using multiple sources of information.
Technical Details of the Attack
Table of Contents
Vulnerability in DAO Maker
DAO Maker’s init() function was exposed, allowing the attacker to reset 4 token contracts with malicious data. Following this, the emergencyExit() function was utilized to extract the funds from each contract.
Four impacted contracts and their respective transactions were:
- 0x6e70c88be1d5c2a4c0c8205764d01abe6a3d2e22: 13.5M CAPS withdrawn
- 0xd6c8dd834abeeefa7a663c1265ce840ca457b1ec: 5M CPD (2.5M CPD withdrawn twice)
- 0xdd571023d95ff6ce5716bf112ccb752e86212167: 1.44M DERC
- 0xa43b89d5e7951d410585360f6808133e8b919289: Approximately 20.6M SHO
Post exploit, the attacker initialized two more contracts.
Another address also displayed a pattern of init()-emergencyExit() calls, hinting at potential whitehat activity or developers attempting to salvage assets.
The attacker eventually traded the tokens for DAI through MetaMask and 1inch
Tokens Involved and their Vesting Contracts
- Four tokens that were affected are: DeRace Token (DERC), Coinspaid (CPD), Capsule Coin (CAPS), and Showcase Token (SHO).
- They all utilize DAO Maker’s vesting system. The vulnerability lay in that the DAO Maker vesting contract could be attacked when DERC tokens were issued.
- A deeper analysis showed that the
initfunction did not authenticate the caller, enabling the hacker to become the owner of the vesting contract.
Detailed Analysis of Contracts and Transactions:
The contracts related to DERC:
- Vesting agency contract: 0x2fd602ed1f8cb6deaba9bedd560ffe772eb85940, 0xdd571023d95ff6ce5716bf112ccb752e86212167
- Vesting implementation contract: 0xf17ca0e0f24a5fa27944275fa0cedec24fbf8ee2
- The attacker’s address was identified as 0x2708cace7b42302af26f1ab896111d87faeff92f
Aftermath of the Exploit
Monetary Impact
The attacker swapped the stolen tokens for DAI:
- Ternoa: 13.5M CAPS for 378,189 DAI on 1inch
- Coinspaid: 5M CPD for 158,216 DAI on 1inch
- DeRace: 1.44M DERC for 997,833 DAI on 1inch
- Showcase: 20.6M SHO for 67,663 DAI via MetaMask Swap Router
As of the report time, token prices had been affected:
- Ternoa CAPS: -45% initially, recovered to -11%
- CoinsPaid CPD: Slumped to -60%, then -25%
- DeRace DERC: Plummeted to -75%, later around -25%
- Showcase SHO: Approximately -75%
Public Response and Opinions
- DAO Maker claimed audits from three firms. However, only one of the audits linked to DAO Maker, and that link from one of them was broken. This raised concerns about transparency and the efficacy of these audits.
- A sentiment emerged, suggesting that while audits are essential, the responsibility for security should lie with the team, not solely with external auditors.
Further Findings
Movement of Stolen Funds
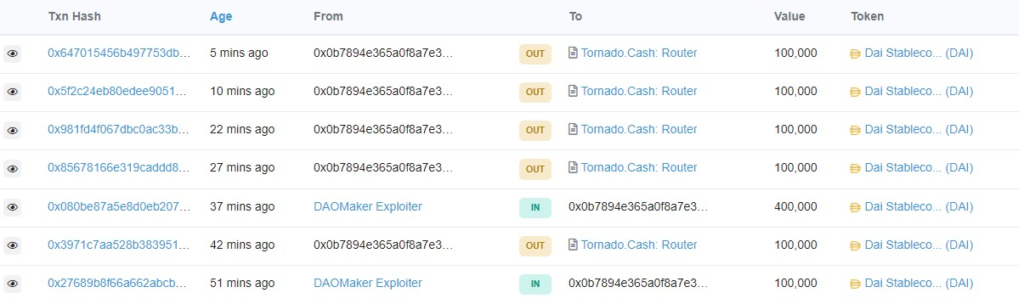
- On September 8 2021, it was confirmed that 500,000 DAI related to the DAO Maker exploit was moved through the Tornado Cash mixing platform, a tool designed to preserve transaction privacy
Connection to Another Exploit
The attacker’s address `0x00a62eb08868ec6feb23465f61aa963b89e57e57` was also implicated in a previous attack on July 14th, targeting the SpaceGodzilla project on the BSC Chain
In SpaceGodzilla exploit, flash loans were leveraged to borrow significant amounts, facilitating price manipulation of platform coins within the PancakeSwap trading pool.
The attacker exploited specific vulnerabilities present in the SpaceGodzilla project, resulting in an arbitrage profit of 25,378.78BUSD.
Conclusions
- The DAO Maker hack unveiled vulnerabilities in its contracts and raised questions about the transparency and reliability of its audit claims.
- The attackers demonstrated sophistication, utilizing platforms like 1inch and MetaMask.
- It’s essential for the community to differentiate DAO Maker from other projects like Makerdao to prevent confusion.
- Efforts should be made to enhance contract security, especially for projects that handle substantial user funds.

