Axion Network launched its new token, AXN on November 2, 2020. However, its price came crashing down as soon as it went live due to a suspected exploit. According to their Telegram channel, Axion Network’s COO reported this was due to a minting exploit in the contract with regards to staking, adding that $500K has been stolen.
The token, as claimed by Axion Network, was not some utility token or an attempt at replacing fiat currencies. It was launched as an investment vehicle that was aimed at one of the biggest untapped markets left in the crypto world: mainstream income investors.
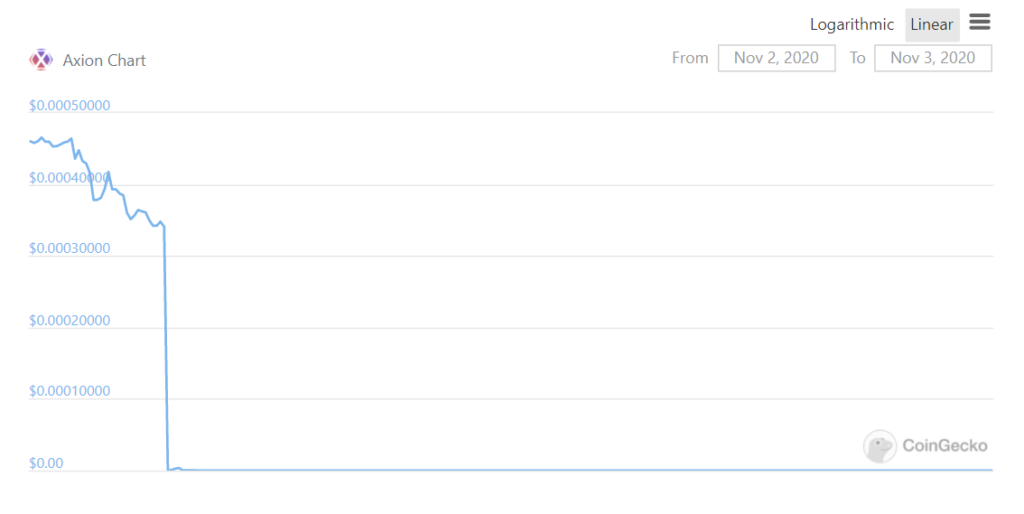
Image Source: CoinGecko
Earlier on Nov 2, the Network went live on mainnet with the AXN token airdrop being made to HEX holders on a 1:1 basis. “70 Billion AXN has already been claimed in the first 20 minutes” tweeted the team.
According to the Axion Network website, well-known smart contract auditing companies, conducted a Smart Contract Code Review and Security Analysis to ensure that our network is tested and secure, thus providing an extremely strong foundation built for longevity. However, even after going through five different audits, the token didn’t even last five hours.
The audit companies for the token reported that they finished the audit in October and the malicious code was added to the smart contract after the completion of the audit, thereafter purposefully injecting the exploit.
They decided to come forth and give an explanation to the community, explaining what they think went wrong and how such attacks can be avoided in the future. As reported, no team members are listed in the project’s white paper or on the website, and the name “Jack Durden” is shared with the unseen narrator from the movie Fight Club.
Deeper into the Hack
Table of Contents
An unknown hacker minted approximately 80 billion AXN tokens by tapping the unstake function of the Axion Staking contract. The hacker then went ahead and dumped the tokens on the AXN Uniswap exchange for Ether, repeating the process until the Uniswap exchange was drained and the token price was driven down to 0.
Hack Txn: https://etherscan.io/tx/0xc2a4a11312384fb34ebd70ea4ae991848049a2688a67bbb2ea1924073ed089b4
According to the token’s audit firm analysis, the attack was likely planned from the inside, involving an injection of malicious code at the time the code was deployed by altering code from OpenZeppelin dependencies.
After investigating the source code of the Smart Contract, it was found that the exploit would cause the sessionDataOf mapping to be affected.
The exploited function was not part of the audit conducted by their team as it was added after joining together Axion’s code with OpenZeppelin’s code via flattening and injecting it within OpenZeppelin’s code before deployment.
Highlights
- The AXN price had a drastic fall from $0.00034079 to $0.00000015, a 99% decrease.
- The attacker netted a hefty 1300 ETH, estimated to be $500K at the time of publication.
- The smart contract was audited five times by big names like Hacken and Certik.
- The exploit was most probably ingested after the audit, right before its deployment.
What went wrong?
Assuming Axion Network committed a mistake, the key takeaway from this incident is to re-audit your smart contracts after even the smallest of changes are done by the developers.
You never know which one of them will initiate the downfall of it all. Re-auditing ensures that the changes you’ve proposed are not affecting the pre-written functions and that there is no chance of encountering an unexpected exploit in the future.
Connect with the team of professionals at ImmuneBytes today to get an audit for your smart contract to avoid any mishaps like these.

