In the world of cryptocurrencies, flash loan attacks are like thieves in the night, silently slipping in and stealing vast sums of digital assets without leaving a trace. These attacks strike quickly and fiercely like a flash of lightning, leaving chaos behind.
For those caught in their path, the consequences can be severe, with financial losses and damage to reputation. Trust in the safety and security of the crypto project can be shattered in a jiffy, leaving all to wonder what will be targeted next.
In most cases, it is the DeFi that fell prey to flash loan hacks, caused by their dependence on unstable price oracles. Price oracles aim to maintain accurate price data of cryptocurrencies, which is used by smart contracts for their appropriate functioning. Insecure oracles are often vulnerable to price manipulation, and can hence lead to hefty flash loan thefts.
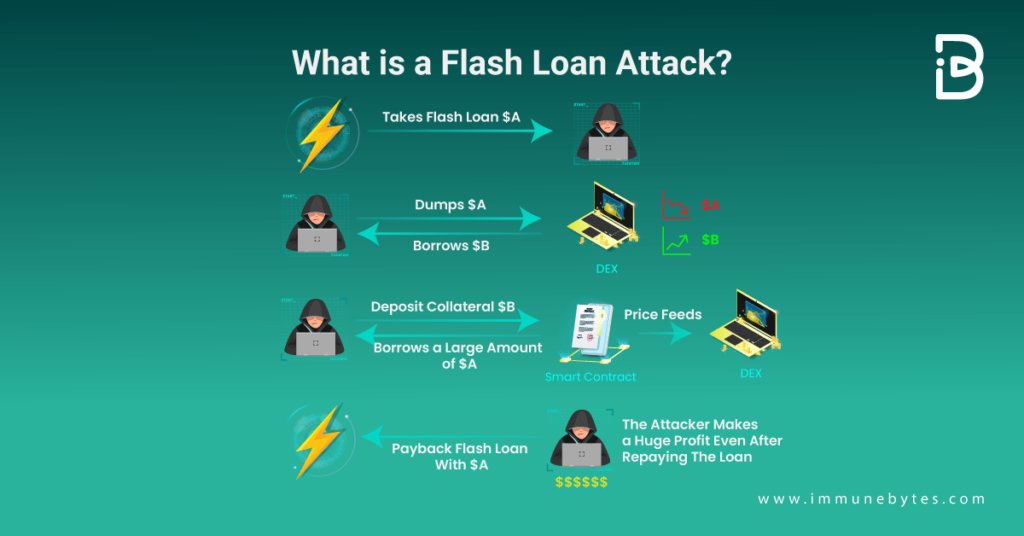
Look at the graphic given below to understand what a flash loan attack is.
Flash loans are a type of short-term, high-risk loan that can be used by cryptocurrency traders to take advantage of temporary imbalances in the market. They allow the borrower to access a large amount of funds for a very short period of time, typically just a few minutes, without having to put up any collateral. These loans are often used for arbitrage and other types of high-speed trading, but they can also be risky because the borrower must repay the loan in full before the end of the loan period, or else face significant penalties.
Moving on to the million-dollar hacks that have been accomplished by flash loan exploits. Below is a list of the top 10 most striking flash loan attacks on smart contracts.
Beanstalk
Table of Contents
Blockchain Protocol: Avalanche
Date of Act: April 17, 2022
Exploit Amount: $181M
Platform Type: Stablecoin protocol
Beanstalk farm lost $182M on April 17, 2022, making it top the list of crypto platforms attacked by the flash loan exploits. It is a stablecoin protocol on Ethereum, whose recently implemented governance mechanism?Curve LP Silos? got compromised.
Aided by the flash loans, the attacker secured significant voting rights. The governance mechanism was then used by the attacker to vote in favor of his own proposal? allowing him to send funds to his wallet address. And post that the flash loan was repaid using the fund amount extracted from the protocol.
Recommended Avalanche Security Services
Cream Finance
Blockchain Protocol: Ethereum
Date: October 27, 2021
Exploit Amount: ~$130M
Platform Type: DeFi
Second, on the list causing a massive $130M loss is Cream Finance? Ethereum’s DeFi platform? which was hacked on Oct 27, 2021. In this case, it wasn’t a simple flash loan attack but was accomplished using complex tactics by the hacker, applying multiple deposits and withdrawals.

In summary, the hacker borrowed $1.5Bn in Yearn protocol’s yUSD vault shares against $2Bn in collateral. He then doubled the value of the shares by donating the same yUSD to yearn vault, making the debt on cream $3Bn against $2Bn in collateral. The $1Bn balance is the hacker’s profit, but since cream had only $130M worth of assets, that became the hacker’s total gain.?
Fei rari
Blockchain Protocol: Arbitrum
Date: May 1, 2022
Exploit Amount:$80M
Platform type: DeFi
On 30 April 2022, Fei protocol? Arbitrum’s DeFi platform? was hacked for over $80M. The attack was an amalgamation of both reentrancy and flash loan exploits.
The Reentrancy security flaw allowed the attackers to borrow assets while withdrawing all the submitted collateral. In particular, the attacker borrowed assets from the pool and flash loaned many tokens/WETH as collateral. The contract’s borrow function was without the check-effect-interaction pattern. It allows the transfer of ETH to the attacker’s contract prior to updating the attacker’s borrow records. The above-given steps were repeated for multiple tokens. Finally, the attacker returned the flash loan and transferred his profits routing through tornado cash.
Pancake bunny
Blockchain Protocol:BSC
Date:May 20, 2021
Exploit Amount:$45M
Platform Type: DeFi
The pancake bunny exploit of May 2021 was accomplished by manipulating its pricing algorithm via 8 flash loan attacks. Using Pancake Swap, the attacker borrowed a significant amount of BNB tokens. These tokens drove BNB’s price against BUSD and $BUNNY. Its native token? $BUNNY? was artificially inflated using these flash loans.
The attacker acquired a significant amount of artificially inflated $BUNNY tokens and dumped them back into the market. This resulted in a price crash of $BUNNY from $146 to $6.17 per token, i.e., a 95% fall.
Recommended BSC Security Audit
Alpha Finance
Blockchain Protocol: Ethereum
Date:February 13, 2021
Exploit Amount:$37.5
Platform Type: DeFi
A sophisticated Defi deception was utilized to steal $37.5 million as a multi-transaction attack was employed to break into Alpha Finance’s vaults.
In the initial phase of the attack, the attacker used UNI-WETH LP as collateral to borrow $1,000e18 sUSD from HomoraBankv2. In order to tamper with internal debt statistics in their system, the attackers’ contract made the Homora code “think ” that their malevolent contract was one of their own. As a result of the exploit, the Alpha Homora governance token ALPHA price fell from $2.25 to $1.78.
Recommended Ethereum Security Audit
Spartan Protocol
Blockchain Protocol: BNB Chain
Date: May 2, 2021
Exploit Amount:$30.5
Platform Type: DeFi
Spartan Protocol a BNB chain DeFi liquidity protocol was sucked out of $30M in a coordinated attack on its liquidity pool.
To claim an excessively large amount of underlying assets, the hacker artificially inflates the asset balance of the liquidity pool before burning the equivalent number of pool tokens.It was due to a smart contract error? the logic used to calculate the liquidity share was itself flawed. The impacted pool suffers a loss of more than $30M as a result of this attack. The asset manipulation was achieved through flash loans of ~$60M in BNB.
Xtoken
Blockchain Protocol: Ethereum
Date: May 12, 2021
Exploit Amount: $24M
Platform Type: Decentralized passive investing protocol
Another Ethereum’s DeFi protocol Xtoken suffered a $24M exploit achieved using flash loans.
A project called xToken automates liquidity and staking mechanisms and wraps them in ERC-20 tokens. The exploit caused a 30% decrease in the platform’s TVL.
The attacker used a dYdX flash loan to borrow >60K ETH, borrowed and swapped for 1.2M SNX tokens, and then sold them on Uniswap to execute the exploit.
Due to the collapse in the price of SNX, the attacker then generated 1.2B xSNXa for just.12 ETH. However, the xSNXa price was high within the xToken protocol, allowing 105M xSNXa to be sold for 414 ETH. After that, the hacker paid back the loans, reversed the swaps, and returned the flash loan to dYdX.
Elephant Money
Blockchain Protocol: BSC
Date: April 13, 2022
Exploit Amount: $22.2M
Platform Type: DeFi
Elephant Money, a stablecoin platform that employs the TRUNK token, was a victim of the flash loan assault, which manipulated a token price oracle, resulting in a $22.2 million loss.
The attacker initially borrowed 91,035,000 BUSD and 131,162 WBNB via the flash loan. The attacker then traded 34,244 ELEPHANT Token for 131,162 WBNB.
BUSD must be deposited in the minting contract in order to start creating fresh TRUNK tokens. After receiving BUSD, the contract converts it to WBNB, which is then used to repurchase ELEPHANT tokens and raise their market value.
The attacker exchanges 34,244 ELEPHANT tokens for 163,782.82 WBNB since he received ELEPHANT tokens with higher market value. Post this the attacker redeemed TRUNK tokens for equivalent WBNB and BUSD. The attacker returned the flash loan, and the remaining was his gain from the hack.
bEarn
Blockchain Protocol: BSC
Date: May 16, 2021
Exploit Amount:$18M
Platform Type: DeFi
In this case, the flash loan was used to exploit the bug in the BvaultsStrategy’s Withdraw function. This incident occurred as a result of faults in the BvaultsBank and its BvaultsStrategy strategy implicitly assuming mismatched asset denominations. Specifically, the BvaultsBank withdraw logic assumes the withdrawal amount is in BUSD, whereas the BvaultsStrategy withdraw logic assumes the withdrawal amount is in ibBUSD. It is worth noting that ibBUSD is an interest-bearing token that is more expensive than BUSD. As a result, a withdrawal request of 100 BUSD results in a withdrawal of 100 ibBUSD. The issue is exploited, and approximately $11 million is drained from the BvaultsBank contract.
Saddle Finance
Blockchain Protocol: Ethereum
Date: May 1, 2022
Exploit Amount:$11M
Platform Type: DeFi
On April 30, 2022, Saddle Finance, an Ethereum-based automated market maker (AMM), was the victim of a series of transactions that exploited deployed smart contracts.
The main error is inconsistencies in how to price calculations of assets within a pool are accomplished. In particular, LP tokens in Meta pools are overpriced in comparison to the underlying asset in the pool. This means that for $1 of a token, you can get more or less than $1 of LP tokens.
The attacker obtained a number of USDCs via flash loan, exchanged them for sUSD, and then exchanged sUSD for Saddle DAI/USDT/USDC LP token via meta pool.
Using the meta pool’s vulnerability LP tokens were exchanged for uUSD, and finally suSD converted to USDC, which were then used to repay the flash loan.
Flash loans have become a norm; they are a part of many severe crypto hacks we have been observing lately. The DeFi concept is still at its nascent stage and is building its place in the financial world. New vulnerabilities are coming up in the decentralized world, which is being exposed by hackers before they are patched.
The only way is to maximize the solutions one has today, including smart contract audits to significantly reduce the errors in one’s code. A smart contract audit is a process in which a team of experts thoroughly examines a smart contract to ensure that it functions as intended and is free of errors or vulnerabilities.
To know more about it visit https://www.immunebytes.com/.

