Although cryptocurrencies are known to exist for decades now, we have seen how their value has taken exponential growth in these years. The crypto industry will sustain in the future as well. Thus, blockchain security services have a lot of importance in today’s world.
The trajectory of cryptocurrencies from being non-conventional investments initially to becoming one of the most omnipotent parts of the international system of payment points towards the utter imperativeness of crypto vulnerability management and having strong security teams.
The continuous integration and deployment of products and applications increase the Software Development Lifecycle’s (SDLC) vulnerability. It is intriguing to see how different organizations are so well-versed with the repercussions of cyberattacks and know everything about blockchain and cybersecurity but still overlook vulnerability assessment.
The implementation and configuration of system security rules and business contingencies are negatively impacted by the lack of a central authority in a decentralized architectural system. The Blockchain system uses the security features already present in the Blockchain technology as a substitute for additional security protection.
Did you know: The financial security breach at PolyNetwork is perhaps the biggest to date? By taking advantage of the Poly Network on the DeFi exchanges Ethereum, Binance Smart Chain, and Polygon, the hackers were able to steal cryptocurrency assets valued at more than $600 million.
This blog will brief you on smart contracts’ different types of crypto vulnerabilities and how to mitigate them.
What is Crypto Vulnerabilities Management?
Table of Contents
It is locating, assessing, prioritizing, and fixing vulnerabilities. Vulnerability management and vulnerability assessment are frequently confused.
Do you know why?
While vulnerability management goes above and beyond by identifying and controlling such flaws, vulnerability assessment is a method for identifying vulnerabilities related to a specific system.
With the new age, people have shifted towards risk-based vulnerability management, a more unique and effective process.
Let us understand what it is and what steps are carried out in this procedure.
5 Stages of Crypto Risk-Based Vulnerability Management
To carry out this process for your organization, you must take the following steps.
Step 1: Discover
Transparency regarding what is in your network is essential since you cannot evaluate what you cannot see. Finding the entire amount of assets in a particular business is the first and most crucial stage in vulnerability management.
Step 2: Assets
Assets must be examined for vulnerabilities after being found. In this stage, vulnerability scans are made to evaluate a group of assets on-demand or regularly.
Step 3: Prioritize
Different vulnerabilities carry different levels of danger for the organization. Prioritizing vulnerabilities is crucial so the team can concentrate on the most critical right now and properly organize the fixes.
Step 4: Remediate
The IT team must repair vulnerabilities following the priority list when they have been prioritized. According to the danger they pose, the patch team is provided a list of vulnerabilities to remedy in this phase, and the fixes are started.
Step 5: Measure and Repeat
To strengthen the security posture and make improvements, specific metrics are crucial. Accordingly, metrics like scanning tactics, time to correct, adherence to industry standards, etc., are changed. This happens again because vulnerability management is a continuous effort.
Best Practices for Secure Coding
There are so many security tools that one can use to ensure secure coding. These include:
- Netsparker
- OpenVAS
- Acunetix
- Intruder
- Aircrack
- Retina CS Community
- Microsoft Baseline Security Analyzer (MBSA)
- Nexpose Community
In addition to these, there are also several practices that you can do to eliminate crypto vulnerabilities. These are:
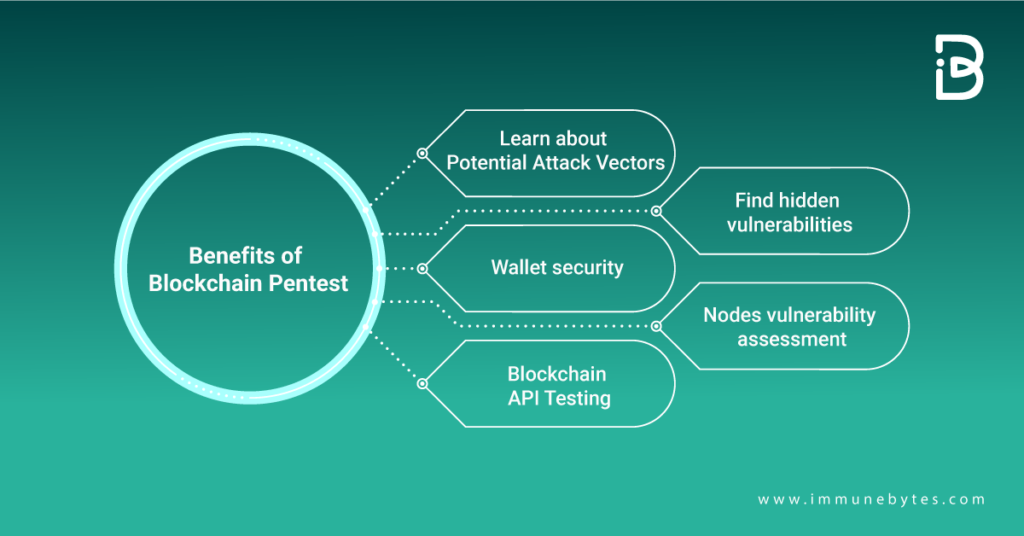
- Penetration Testing
- Putting identification and access control policies into practice to limit access
- Using Hardware Security Module (HSM) to ensure the security of Blockchain identity keys.
- Enforcing identification, authentication, and authorization for all APIs to secure transactions that use them.
- Putting in place Privileged Access Management (PAM) to provide appropriate individuals access to administrative needs
- Employing technologies that protect privacy and classify data to protect sensitive information.
- Using access control to secure all facets of smart contracts.
Additional Resource: What is Penetration Testing?
List of Different Types Of Crypto Vulnerabilities
Other elements that make small and medium-sized firms vulnerable to cyber assaults include the lack of awareness in various organizations and the misunderstanding of threat vulnerability. Risk management is essential since firms are incorporating cryptocurrency and other crypto assets.
Therefore, let’s look at certain blockchain weaknesses and how cybercriminals might use them:
Blockchain Network Attacks
Hackers search for network weaknesses and use Distributed Denial of Service (DDoS), transaction malleability, Sybil, routing, eclipse, and long-range attacks against networks using the PoS consensus method targets. In addition, hackers can manipulate the node’s network time counter to force it to accept a different blockchain by taking advantage of the cryptocurrency timestamp handling.
Smart contract attack
Hackers use developer flaws in coding to launch attacks on smart contracts on the Ethereum Blockchain. To prevent exploitation, these contract developers must fix security weaknesses during the development and execution phases.
To prevent any unlawful use of the Ethereum-based Smart Contract coding, attention must be paid to software creation, updating, and maintenance.
Recommended: What is Smart Contract Security Audit?
User-wallet attacks
Cybercriminals frequently target the login information for users’ Blockchain wallets. They employ phishing, incorrect key creation, hot and cold wallet attacks, and dictionary assaults to obtain user credentials. Hackers can take advantage of blockchain networks’ weak user signatures by utilizing different cryptographic techniques.
Transaction verification attack
Only when all nodes concur, do transactions become confirmed on the blockchain. This lengthy verification method develops a weakness for hackers. A 51% attack on Ethereum Classic (ETC) in August 2020 resulted in the double spending of more than $5.6 million in cryptocurrency. In August 2020, a 51% assault on Ethereum Classic (ETC) led to the double spending of more than $5.6 million worth of cryptocurrency.
Wrapping up
Cryptocurrencies are a desirable target for cybercriminals due to their rising value. To survive in the volatile currency environment, businesses must master the fundamentals of Blockchain tracking and cryptocurrency transactions.
To properly apply cybersecurity measures, it is also vital to comprehend the security threats related to cryptocurrency assets and Blockchain systems. The Blockchain system and its users must be protected using various security techniques and strict quality control guidelines.
Additional Resources
Common Smart Contract Vulnerabilities
Traits of Good Cybersecurity Company

