Once again we have a BSC-based DeFi protocol, Spartan, falling prey to the hands of hackers! The attacker exploited a flaw in the smart contract that governs the Spartan Protocol, depriving them of more than $30 million.
Spartan Protocol is a community-governed token to incentivize deep liquidity pools for leveraged synthetic token generation. Similar to the Ethereum-based Synthetix, the Spartan project aimed to create synthetic tradable assets that reflect the value of other assets. It is a token based on the Binance Smart Chain in light of allowing its users near-instant settlement and extremely low gas fees.
The attack happened just a few days after another DeFi protocol was attacked on Binance Smart Chain. The Spartan team confirmed the hack in a tweet, stating, “Spartan Pools v1 exploited – the team is aware and investigating.”
In this blog post, we elaborate on the technical details of the hack.
Technical Breakdown of the Incident
Table of Contents
Initiated at 04:38:39 PM +UTC, May 1, 2021, the Spartan protocol contract was exploited to result in more than a $30M loss. The incident was due to a flawed liquidity share calculation in the protocol, which is exploited to drain assets from the pool.
Similar to the Uranium Finance incident, this hack inflates the asset balance of the pool before burning the same amount of pool tokens to claim an unnecessarily large amount of underlying assets.
There were a total of 9 attacks on four Spartan Protocol pools. The details are as follows:

Let’s get an insight into how the attack proceeded.
- For the first attack, the hacker uses a 100k WBNB flash loan, and for subsequent, swaps their own WBNB to second tokens in pools.
- It swaps WBNB to SPARTAN five times through the exploited Spartan pool! In order to bypass the built-in slippage mitigation measure, repeated calls are used.
- Then it sends tokens and SPARTA to pools and calls the added liquidity() to mint LP tokens.
- It inflates the asset balance in the pool by transferring it into the pool.
- It then burns the pool tokens obtained from step 2 to withdraw the liquidity.
- Moving further, it adds liquidity into the pool with the added assets in step 4 with the pool token, which is immediately burned to obtain fair amounts of SPARTA and WBNB.
- It repeats the above steps to continue draining funds from the pool.
- It returns the flash loan with 100,260 WBNB!
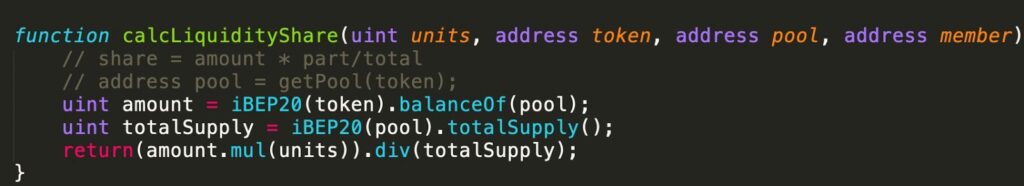
The vulnerability emerges from the fact that the liquidity share calculation calcLiquidityShare() is querying the current balance which can further be inflated for manipulation. A correct calculation should make use of cached balance in baseAmountPooled/tokenAmountPooled.
The Aftermath
This attack on Spartan Protocol makes it the sixth-biggest monetary exploit in DeFi history, according to Rekt.
The price of the Spartan Protocol’s SPARTA token dropped from $US1.66 to as low as $US1 over the weekend but had rebounded Monday, trading at $US1.36 at the time of writing.

The Spartan team claimed that the code was audited and yet it had a flaw. Quoting the team, “Sparta will re-build with more focus on continual reviews. Sparta is innovative code, built from scratch, it is not a clone of anything.”
Spartan’s team will now be focussing on getting the remaining funds back to members involved by working with Binance on the recovery of stolen funds. Also, they plan to Get back to shipping V2!
Highlights:
- BSC’s Spartan Protocol was hacked for more than $30M due to a miscalculation in the protocol’s liquidity share.
- The attack is quite similar to the Uranium Finance hack which happened last week.
- There was a flaw in the smart contract code which was audited.
- The Spartan team is working on getting the maximum funds returned.
The attacks on the Binance Smart Chain seem to be increasing with each passing day! Once hailed unbearably, BSC is now swimming through some tough waters! The only thing that can save you is getting a security verification done! Know your audits and auditors, do not shy away from the requirements of your project. The ImmuneBytes team makes it a priority to understand your code and ensure that it works as intended!
Recommend for BSC Token Audit
About ImmuneBytes
We are a team of India-based security professionals who are skilled and hold experience in their niche. With us, you’ll never have to compromise. We strive to push forward and provide overall surveillance and quality service to our customers. Get in touch with us to get a security audit for your smart contract.

