Have you ever wondered how a hacker is able to drain millions of dollars from a company? Or how the biggest of organizations suffer because of one loophole in the system? How a tiny error can cause the whole project to fail? Well, let’s find out how.
Blockchain is considered to be the most secure platform in today’s day and age, or so we thought. However, much to our disappointment, the impenetrability of blockchains isn’t living up to the hype and bugs are more common in blockchains than we had thought. It’s because sometimes even the largest organizations and the most experienced developers make mistakes. Consequences? Loss of millions.
2019 saw more cryptocurrency attacks than any other year. Be it 51% attacks, exchange hacks, social engineering issues, and whatnot. These attacks not only affect the companies but also the investors. The attitude towards the adoption of blockchain technology has been remotely slow because of this very reason.
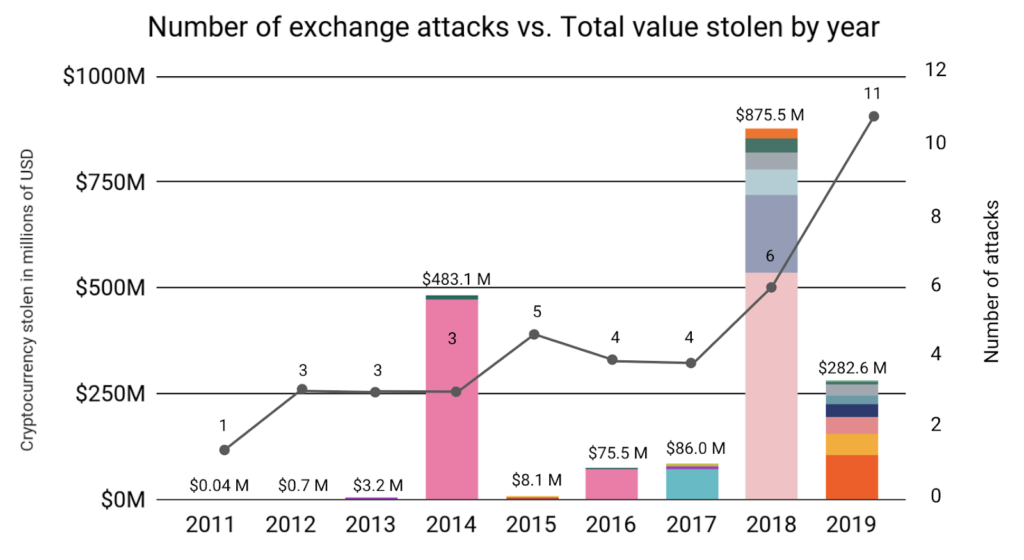
Source: Chainalysis
Should you be worried? Yes. Hackers will continue to find creative ways to breach the system and even reinvent newer attacks to cause disruptions. But the bigger question here is, What should you do?
How to NOT Get Hacked?
Table of Contents
One of the smart things to do here is to get an audit for your smart contract by a third party.
Auditing your smart contracts will not only secure your project but it’ll also help your investors/users by building their confidence and establishing a trust setup between your organization and theirs.
ImmuneBytes is a well-known organization that provides you with professional services in the blockchain space. Our team has hands-on experience in conducting smart contract audits. Our team is actively contributing to the DeFi space and other major blockchain frameworks. We have been able to secure? 175+? blockchain projects by providing security services on different frameworks. Connect with us today to get an audit for your smart contract.
In the meantime…
We are coming up with a new series that is going to help you in understanding the most commonly overlooked bugs in smart contracts.
What to Expect?
This series is going to provide you with the basic knowledge about the different types of vulnerabilities and loopholes that you may have not noticed before. We will be discussing the different types of bugs, doing their technical analysis for you, and giving you at least one real-life example. The bugs that we will be covering are:
- Flash loan attacks
- Re-entrancy?
- Time Dependency
- Integer Overflow and Underflow
- Stack Size Limit
- Transaction Ordering Dependency
- Delegate Call Return Value
- Race condition
- Unpredictable state
- Ether lost in the transfer
- Uninitialized Storage Parameters
- Tx.origin
- External contract referencing
- High order byte clean storage
- Transfer forward all gas
ImmuneBytes continues to facilitate different ways to ensure safety and security in the DeFi world. We are really excited about this series and we hope you are too.?
Stay tuned for the next part of this series in which we explain Flash loan attacks and what major setbacks it has caused in the crypto world.
And if you wish to learn more about Smart Contract Security, you can read our?latest blogs.

