2022 has proven to be quite a promising year for the DeFi ecosystem. Significant milestones were achieved, including reaching close to $40 billion in total locked value in DeFi. The returns on DEX tokens also increased by 5x as compared to the centralized exchange tokens.
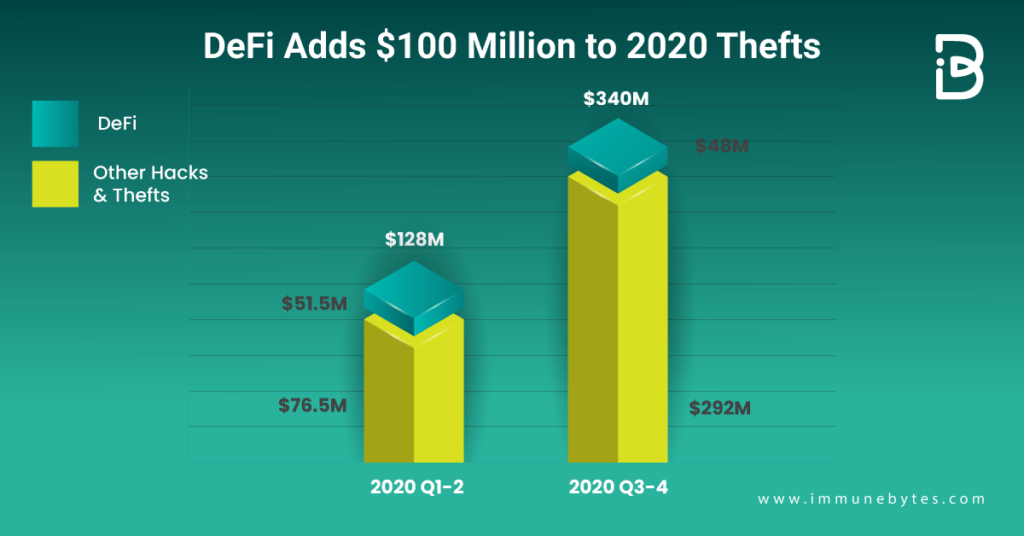
However, with the industry thriving, the number of hacks and breaches hasn’t come to a halt. If nothing, 2020 saw a considerable increase in the number of DeFi security breaches. Reports say more than half of the crypto hacks in 2020 were from DeFi exchanges and protocols.
ImmuneBytes published a comprehensive list of all the crypto attacks that happened last year, read the full article here.
One might ask, what could be the reason for the rising number of hacks? We say, one of the many notable reasons is the lack of credibility given to third-party security audits and the reliance of the DeFi industry on unaudited code.
?Auditing is not a silver bullet, and not all audits are equal, but it is a crucial step for any DeFi contracts before deployment.?
What is a DeFi Security Audit?
In simple terms, a DeFi audit is a comprehensive assessment of the code by professionals to point out the potential threats in your smart contract. There are several threats that a DeFi application is exposed to, such as re-entrancy attacks, DoS attacks, front-running, etc, which can be mitigated if the code is audited. Audits help to detect uneven and unexpected vulnerabilities of smart contracts before project deployment and therefore, prevent DeFi hacks.

The ultimate goal of a DeFi security audit is to guarantee that the code is free of bugs and behaves as intended, under every given circumstance. A completed audit means that the code was reviewed, though the rigorousness of the audit may vary substantially ? and this rigor is what matters for security, not merely the presence of an audit.
Steps Involved in a DeFi Audit
The process of auditing DeFi exchange contracts covers four major dimensions of users? privacy? defense of private key architecture security, business logic, data maintenance, and infrastructure to ensure the safe and stable operation of the exchange business.
To categorize the auditing process into concrete phases, we have:
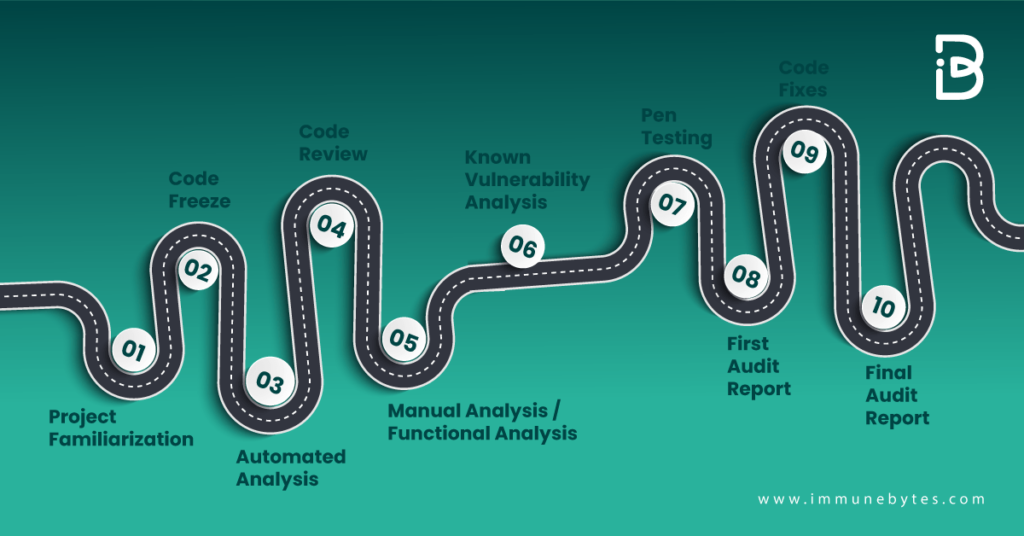
Project Familiarization
Before starting to dig into the code, the auditors will want to sit with the development team to understand the underlying architecture and intended behavior of the smart contract. Whitepapers and detailed documentation prove to be quite helpful in this phase.
Code Freeze
Code Freeze is nothing but simply when the developers decide on the final code for the contract. The code, then, can’t be subjected to any more alterations.
Code Review
In the code review step, the auditing team will look more closely into the code for a complete understanding. This can include the design and which libraries the developers used, checking the test coverage, and how the project is intended to function.
Automated Analysis
Concerning certain business logic, Top smart contract auditors conduct automated assessments using dynamic analysis tools such as? MyThrill, Hyperledger Caliper, Manticore, etc. In the initial steps, identification of bugs in the test suite that is critical to the application is highly advisable.
Manual Analysis / Functional Analysis
Automated analysis sometimes reports false positives, which is why it is always a good practice to manually review the code. It also applies the usual software guidelines such as commenting code, code structure, naming variables, and the avoidance of replicated code.
Known Vulnerability Analysis
For an audit to be called a ‘smart? audit, this step becomes an ultimate necessity. Some vulnerabilities surface time and again in the crypto-world, thus it seems only wise to separately test for them. These known vulnerabilities include? re-entrancy, gas limit issues, timestamp dependencies, and others.
Recommended Coin Audit
Pen Testing
Auditors can sometimes opt for deploying the code on a local testnet to run their tests or perform their white-hat attacks.
First Audit Report
After all these steps are completed, smart contract auditors will write down the findings and recommendations in a report for their clients to review.
Code Fixes
After the first audit report, developers make the necessary changes and fixes to the code and turn it up again for a final review by the auditors.
Final Audit Report
After all the fixes are done, auditors combine all the details and analysis into a report and submit it to the client.
Although these steps may vary depending upon the auditing team, at ImmuneBytes we make sure to follow a strict methodology comprising of the above-mentioned steps while conducting the audit.
Final Thoughts
Despite the increase in security breaches, the sun still shines bright for the DeFi industry and it continues to receive an overwhelmingly optimistic response from the people. As far as statistics are concerned, they show positive growth.
Auditing companies should start working closely with the community and adapt to this new landscape for the community to continue its growth rate. Regardless of what level of the stack you’re working on, smart contract security must be a top priority for those interested in securing the future of DeFi.
About ImmuneBytes
We are a team of India-based security professionals who are skilled in their niche. We strive to push forward and provide overall surveillance and quality service to our customers. We ensure the security of your project and allow business owners to run their blockchain applications hassle-free. We’ve been hired by over 175+ blockchain startups and corporations to make their audit of smart contracts at an affordable cost.

